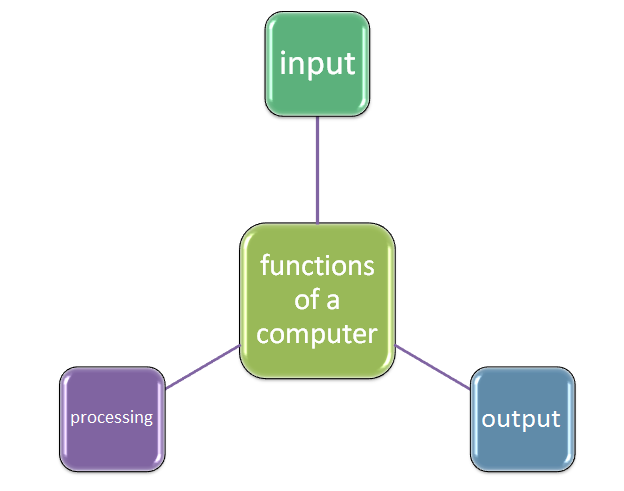
1. inputThis is the ability for a computer to accept data either through input devices such as scanners, keyboards, mice and others or through information retrieved from storage devices. Input of data is a main function because all other functions depend on the incoming data for processing and output. 2. processingProcessing and storage are sometimes broken down as separate basic functions of a computer. However, looking at this critical idea keenly, we notice that processing and storage are sometimes inseparable this is because processing devices rely heavily on storage devices vis a vis. Processing is an act where a computer converts raw meaningless piece of information called data into a more meaningful piece of information. This is normally done with a closer help of primary storage devices such as the RAM, and special types of memories such as the registers, buffers and cache memory. Processing is a main function of a computer because of the conversion, manipulation of numeric data and logical decisions. 3. OutputThis is an act for a computer to display the result of a processing activity. This can be done using output devices such as the monitor, printer, plotter, speakers etc.
The functions of a computer system cannot be complete without the output, simply because it gives a feedback of the result for the computer user to digest, change, amend, store or print.
0 Comments
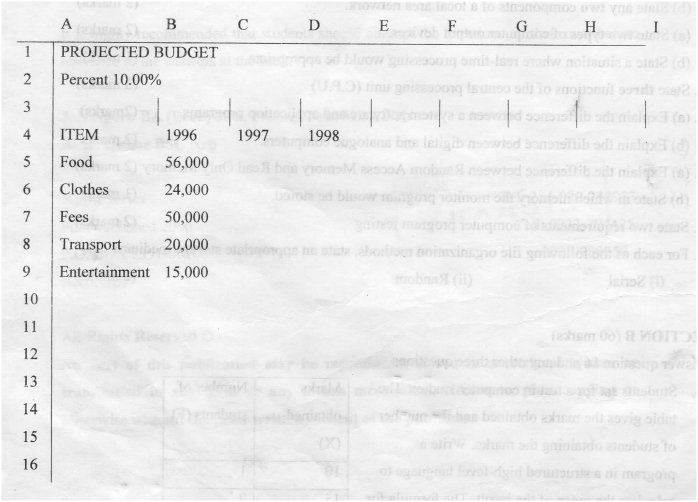
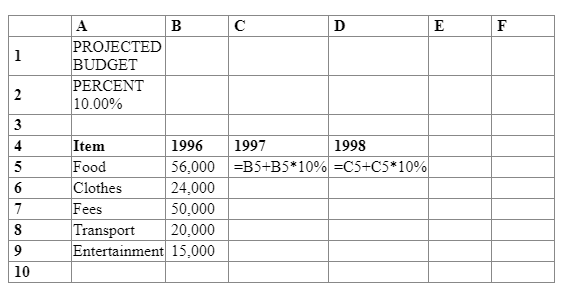
A spreadsheet has the following entries. Provide a formula for cell c5 that can be copied onto cell d5 and the range c6...d10 to give a uniform increase of 10% of the previous years value for each item. Expected responseWhat is a laser printer?This is an electrostatic technology powered printer that uses a laser beam of light to create characters on a piece of paper. How a laser printer works
RELATED LINKS ..Advantages of laser printers
Disadvantages of laser printers
wHAT ARE SECONDARY sTORAGE DEVICES?Also called auxiliary storage devices or persistent storage media are computer hardware devices involved in the storage of data, permanently. These devices can be categorized as: Related links ..
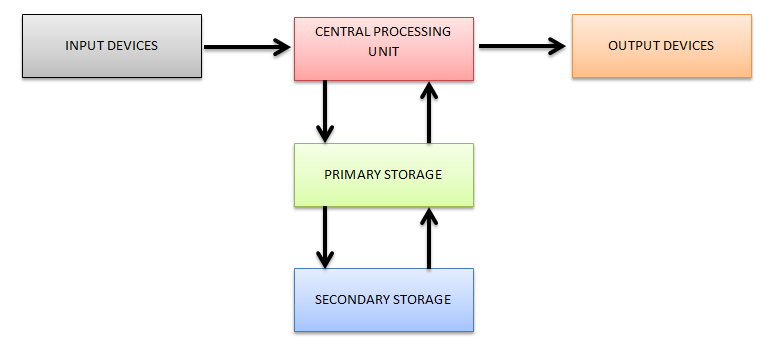
DRAW A DIAGRAM SHOWING THE FUNCTIONAL UNITS OF A COMPUTER HARDWARE. NAME THE UNITS01. INPUT DECICES
These are devices that enter data into a computer and also covert data from human readable form to machine readable form.
Examples of these devices include:
02. Central Processing unit
The CPU-Central Processing Unit is a device made from a collection of integrated circuits. Its main functions are:
03. Primary Storage
These are devices that provide temporary storage for task that are to and from processing. They include:
04. Secondary Storage
These are devices that permanently store data in the computer or they are portable. They include:
Related Searches:
05. Output Devices
These are devices that display activities in the CPU to the user and converts information from machine readable form to human readable form. These devices include:
In the evolution of computers, each of the passing computer generations had its own technology which was an improvement of the previous technology. Below is a match of computer generations with their processor technology and what each of the processors were capable of.
01. FIRST GENERATION COMPUTERS
They used thermionic valves
This is a device that controls electric current flow in a high vacuum between electrodes to which an electric potential difference has been applied. as a thermionic tube or thermionic valve uses the phenomenon of thermionic emission of electrons from a heated cathode and is used for a number of fundamental electronic functions such as signal amplification and current rectification. [Source: https://en.wikipedia.org/wiki/Vacuum_tube] 02. SECOND GENERATION COMPUTERS
They used transistors
A transistor is a semiconductor device used to amplify or switch electronic signals and electrical power. It is composed of semiconductor material usually with at least three terminals for connection to an external circuit. How does a transistor work ? By turning a small input current into a large output current, the transistor acts like an amplifier. But it also acts like a switch at the same time. When there is no current to the base, little or no current flows between the collector and the emitter. Turn on the base current and a big current flows. [Source: https://www.quora.com/What-is-the-use-of-transistors-in-a-circuit#] 03. THIRD GENERATION COMPUTERS
They used Integrated Circuits (ICs)
A collection of transistors make up an Integrated Circuit An integrated circuit (IC), sometimes called a chip or microchip, is a semiconductor wafer on which thousands or millions of tiny resistors, capacitors, and transistors are fabricated. An IC can function as an amplifier, oscillator, timer, counter, computer memory, or microprocessor. A particular IC is categorized as either linear (analog) or digital, depending on its intended application. [Source: https://whatis.techtarget.com/definition/integrated-circuit-IC] 04. FOURTH GENERATION COMPUTERS
They used very large scale integrated (VLSI)
VLSI is an acronym that represents Very Large Scale Integrated. A collection of Integrated Circuits (ICs) Make up VLSI An Integrated Circuit is the circuit in which all the Passive and Active components are fabricated onto a single chip. Initially the Integrated Chip could accommodate only a few components. As the days passed, the devices became more complex and required more number of circuits which made the devices look bulky. Instead of accommodating more circuits in the system, an Integration technology was developed to increase the number of components that are to be placed on a single chip. This Technology not only helped to reduce the size of the devices but also improved their speed. Depending upon the number of components (Transistors) to be integrated, they were categorized as SSI, MSI, LSI, VLSI, ULSI & GSI. Small Scale Integration (SSI):
What is an operating system
An operating system is a collection of integrated computer programs that provide recurring services to other programs or to the user of a computer.
These services consist of disk and file management, input/output activities, storage resources, diverse support services and control of various resources.
Ssmengg.edu.in describes an operating system as a program that acts as an intermediary between a user of a computer and the computer hardware. it further adds "the purpose of an operating system is to provide an environment in which a user can execute programs and the primary goal of an operating system is thus to make the computer system convenient to use."
Tutorial point describes an Operating System (OS) as an interface between a computer user and computer hardware. An operating system is a software which performs all the basic tasks like file management, memory management, process management, handling input and output, and controlling peripheral devices such as disk drives and printers.
Some popular Operating Systems include Linux Operating System, Windows Operating System, VMS, OS/400, AIX, z/OS, etc. factors to consider when choosing an operating system
dEFINITION OF dISTRIBUTED SYSTEMS
A distributed system is a collection of computers on the same network which process data independently and once data has been updated in one computer, other computers of the same system automatically update their database too.
A distributed system can also be defined as a collection of independent computers that appears to its users as a single coherent system Distributed processing refers to the type of processing where computers in various geographical locations are interconnected via communication links for the purpose of local processing and data access and/or transfer. In distributed processing data processing occurs on each of the computers, unlike a centralized processing system in which terminals are connected to a host computer that performs all of the data processing. Advantages of distributed systems
Disadvantages of distributed system
Works Cited
USES OF COMPUTERS IN HEALTH SYSTEMS01. KEEPING OF RECORDS
02. RESEARCH
03. TRANSACTIONS SUCH AS HOSPITAL BILLS
04. SECURITY
05. DIAGNOSING PATIENTS
06. AUTOMATING LIFE SUPPORT MACHINES
07. LABORATORY ANALYSIS
08. PREPARING AND ANALYSING REPORTS
09. COMMUNICATIONS
10. SUPPORTING HOSPITAL INFORMATION SYSTEMS
meaning of data privacyData privacy means that data or information belonging to an individual should not be accessed by or disclosed to other people. Its an individual's right to determine for themselves what should be communicated to others. meaning of data securityData security is the confidentiality, integrity and availability of data. Confidentiality of data implies that sensitive data or information belonging to an organization or government should not be accessed by or disclosed to unauthorized people, such data includes office documents, chemical formula, employee's details, examinations etc. Integrity of data implies that data should not be modified without owner's permission. Availability of data implies that information must be available on demand. DISSIMILARITY between data privacy and data security
Why should people resist computers in their work place?01.
Computers may lead to job replacement and displacement.
This means that computers may make a person lose his/her job or root for the transfer of a worker to another department. A condition like this one may make people resist computers at their work place. 02.
Computers require skilled manpower.
Usage of computers requires the staff to be trained for necessary skills to handle them. For those who don't see training as a good idea, will resist its implementation in a work place. 03.
Computers have adverse effects on our health.
It is believed that computers cause cancer, electromagnetic radiation, changes in brain activity, eye problems and sleeping patterns. However, scientists are still researching on these areas to establish elements of computers that are responsible for these problems and how they can be avoided. 04.
Some people are just bureaucratic.
Some people in work places are just difficult to change, they follow excessively complicated administrative procedures that demands things to be done they way they used to be. Examples of these bureaucrats are school heads who demand professional records to be handwritten rather than being typed and printed. They think that handwritten records are more original than the printed ones. These are the kind of people who will never tolerate computer changes in their institutions. 05.
Attitude problems leading to computer-phobia
There are certain personalities who just hate computers because they either acquired this attitude myth or had previous shallow experience with computers. These people may likely resist the introduction of computers in their workplace and if it is introduced, they will blame it for everything bad that happens. 06.
Fear of increased work in their workplace
Computers sometimes increases the amount of work in a work place. This is especially if new programs and applications are added to be used by the system. And if there will be no addition of manpower, handling them on top of your normal tasks can sometimes be overwhelming, in this case, people tend to resist them in their work places for fear of additional tasks. 07.
Fear of increased initial costs
Introduction of computers require high initial costs however their benefits outweigh the costs (cost effectiveness). Some people may oppose implementation of computers in their workplace simply because they fear the initial costs. 08.
Poor communication skills/strategies
Bad communication skills from the top management to workers below them may trigger workers to resist technology change. Communication breakdown, misinformation or inaccurate communication can be a recipe on why people may opt to resist technological change. Changes that are mandated with little or no communication, on the other hand, are often poorly received, since employees may feel that the change is being shoved down their throats. When it comes to change management there’s no such thing as too much communication. If there is no immediate information to communicate during the change, telling employees that there is no update regarding the ongoing change is communication! Don’t just keep quiet; this is also the time to maintain an open door policy regardless of where you are placed in the organization. 09.
The Rapid Pace of Change
People often reject technology because it presents changes, big or small, to their immediate world, a world to which they have worked hard to adjust. People usually resist to anything that disturbs their social order and if done rapidly, change may never be taken seriously, this can lead to drastic opposition and resistance. 10.
Poor Timing:
This is another viable reason why employees resist introduction of computers at work. Change must be introduced when there are no other major initiatives going on. Sometimes it is not what a leader does, but it is how, when and why she or he does it that creates resistance to change! Undue resistance can occur because changes are introduced in an insensitive manner or at an awkward time. Works Cited
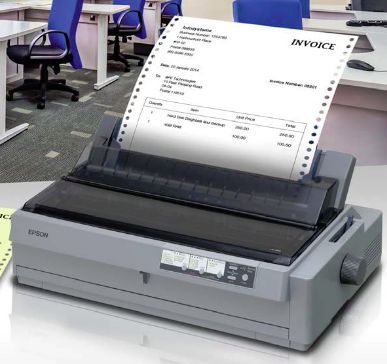
What it means by printing multiple copiesPrinting multiple copies implies that two or more papers are printed at the same time by only one printer. This is only possible by the use of impact printers such as a dot-matrix and a daisy wheel printer because they have special hammers that produce characters on a piece of paper. And behind every paper, there is a coupon copy that produces characters on another paper. This type of printing is majorly done where monetary transactions are carried out such as a bank. For example; when paying school fees through a bank, the bank produces three copies of receipts (whitish, blueish and pinkish) in color. One copy for the bank, another for the school and the last one for your own records. To produce these receipts (vouchers/slips), the bank prints them in multiple copies using impact printers. What it means by printing multiple pagesPrinting multiple pages is a situation where printers automatically make characters on a piece of paper (one paper at a time) but automatically pulls the next paper in a series once the current is over, this process repeats until the printing task is accomplished. Printing multiple pages depends on the printing mechanism of the printer. There are those printers that can only print one side of the page at a time and others reverse the page to print on the other side. It is called back to back printing. Any type of printer can handle multiple page printing, however the desk-jet printer and laser-jet printers are preferred for this job because of their printing speed. Images courtesy of Pinterest
FORMATTING FEATURES OF WORD PROCESSORSwHAT ARE FORMATTING FEATURES?
These are word processor enhancements that makes user's work appealing to the eye.
What are these formatting features?
Font color is used to change text color
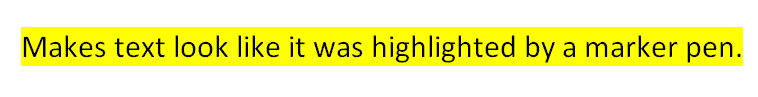
Makes text look like it was highlighted by a marker pen.
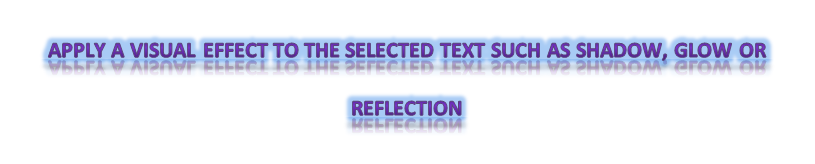
Apply a visual effect to the selected text such as shadow, glow or reflection
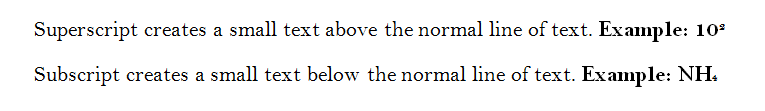
Superscript creates a small text above the normal line of text.
Subscript creates a small text below the normal line of text.
Draws a line through the middle of the selected line
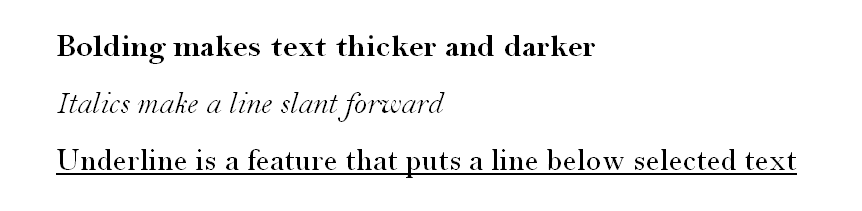
Bolding makes text thicker and darker
Italics make text slant forward Underline is a feature that puts a line below selected text
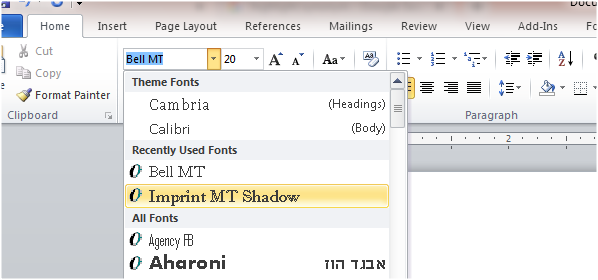
this is a feature used to change text font themes
this is a feature used to increase
or decrease the size of text
Numbered list is a feature that index items in numbered style e.g.
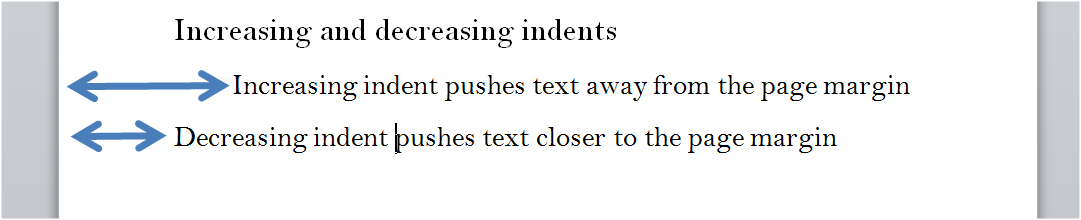
Increasing indent pushes text away from the page margin
Decreasing indent pushes text closer to the page margin
this is a formatting feature used to increase or decrease spaces between lines of text and paragraph
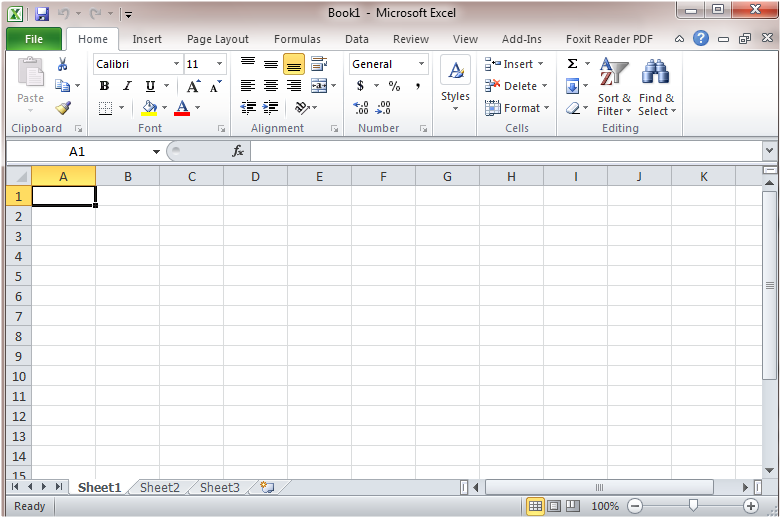
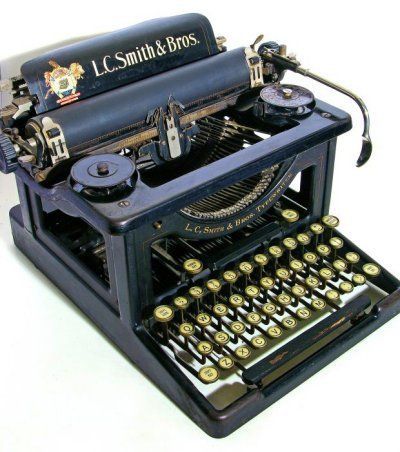
WHAT ARE ELECTRONIC SPREADSHEETS?WHAT ARE TYPEWRITERS?WHAT ARE THE MERITS OF SPREADSHEETS OVER TYPEWRITERS?
Images courtesy of Pinterest
|
Categories
All
Archives
December 2024
|
Can't find what you are looking for? Don't worry, Use the Search Box Below.
|
Primary Resources
College Resources
|
Secondary Resources
|
Contact Us
Manyam Franchise
P.O Box 1189 - 40200 Kisii Tel: 0728 450 424 Tel: 0738 619 279 E-mail - sales@manyamfranchise.com |



 RSS Feed
RSS Feed

