(a) A company has decided to computerize their operations. They have decided to purchase packages instead of developing their own programs. Give three advantages and two disadvantages of this approach.
Advantages
0 Comments
(a) Give three examples of network software
A computer specification has the following details:
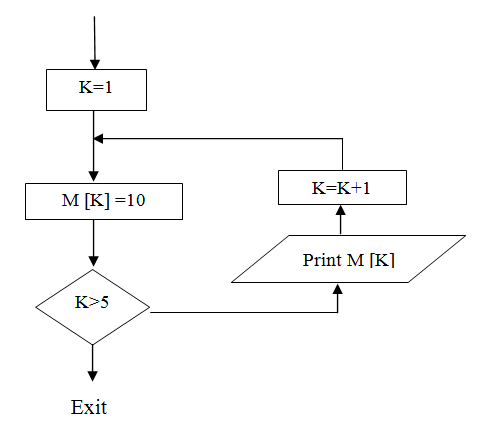
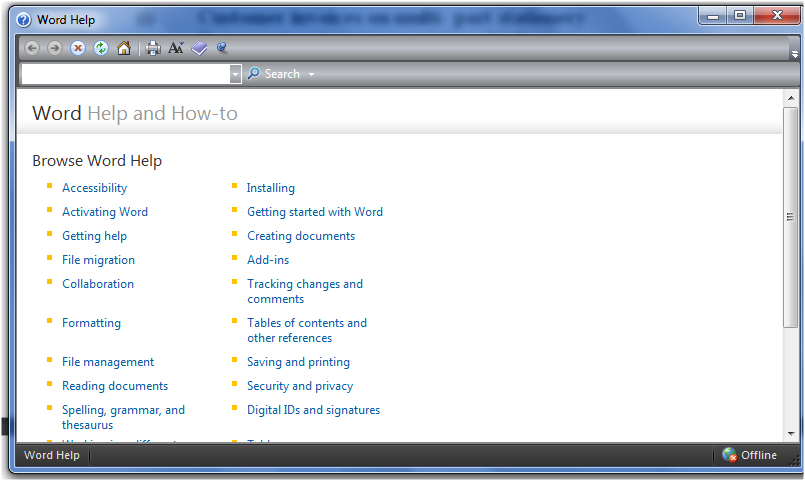
Study the flowchart below and answer the questions that follow (a) Write a high level language program for the above flowchart (7mks)Name two features of database package
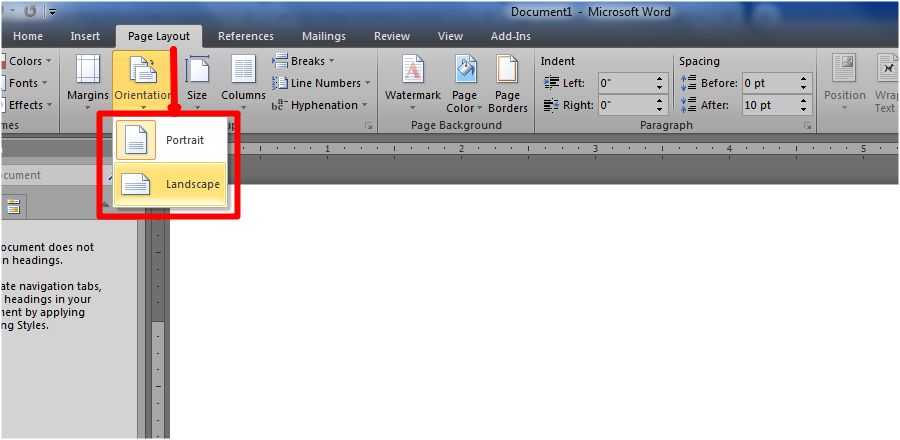
(a) Name two methods of paper orientation (1mk)
(b) Name two keys used to delete text in a document (1mk)
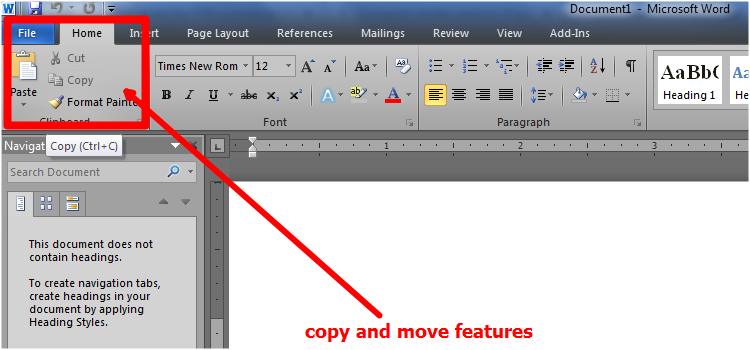
Distinguish between copying and moving text
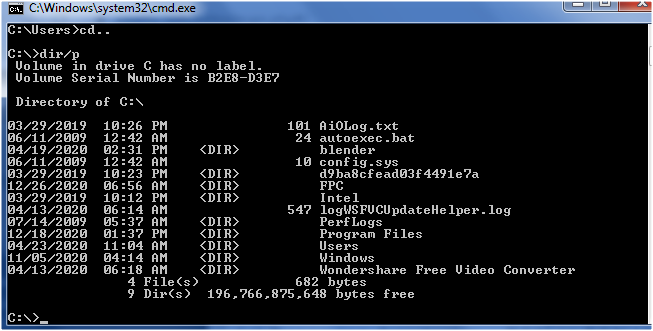
What are the DOS commands used for the following?
(a) Changing directories – CD\ (b) Viewing directories – DIR (c) Renaming directories – REN or RENAME (d) Deleting a directory- RD\ Give two reasons why optical disks are better storage media compared to floppy diskettes (2mks)
(a) What is an expert system (1mk)
A software consisting of knowledge and rules for using it gathered from human experts in a particular occupation e.g. medicine. An expert system has the capability to store the collection of knowledge & manipulate it in response to user inquiries
(b) State any two components of an expert system (2mks)
Study the flowchart segment below and state the last value printed from the flowchart. (2mks)
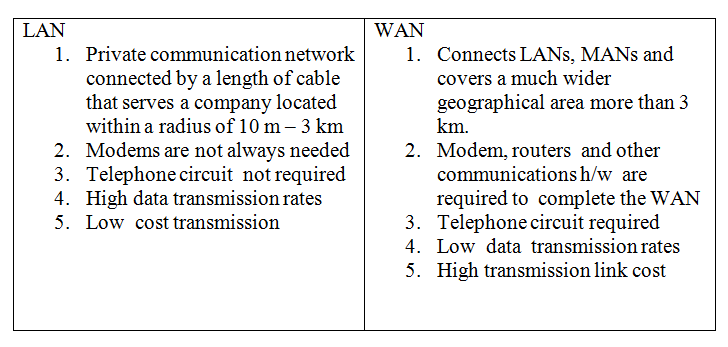
List three differences between Wide Area Networks (WAN) and Local Area Networks (LAN) (3mks)
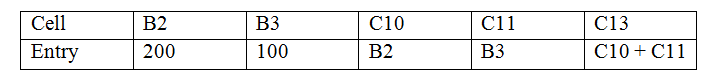
(a) Distinguish between labels and formulae with respect to spreadsheet (2mks)
(b) Consider the entries in the cells below(c) State the values displayed in cell C14 (2mks)
Error (#value) NB: the = sign is missing in cells C10 and C11
State any two features of a user- friendly program
Briefly explain the purpose of the following types of program documentation
(a) User manual
(a) Distinguish between machine and assembly language (2mks)
(b) State the type of translator necessary for a program written in:
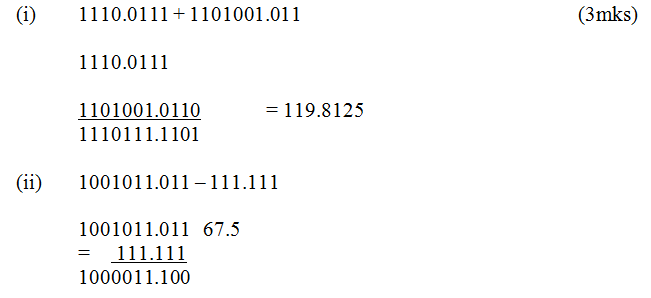
(a) Explain the term nibbles as used in data representation in computersA nibble refers to a half a byte or 4 bits ( A byte is equivalent to 8 bits) (b) Perform the following binary arithmetic giving the answers in decimal notation.
(a) State two tasks of a processor (2mks)(b) State the functions of I/O devices
|
Categories
All
Archives
December 2024
|
Can't find what you are looking for? Don't worry, Use the Search Box Below.
|
Primary Resources
College Resources
|
Secondary Resources
|
Contact Us
Manyam Franchise
P.O Box 1189 - 40200 Kisii Tel: 0728 450 424 Tel: 0738 619 279 E-mail - sales@manyamfranchise.com |







 RSS Feed
RSS Feed

